Poland Cyber Threat Assessment - January 2026
Comprehensive analysis of hybrid warfare operations targeting Poland. Intelligence derived from Baysec CTI and open-source reporting.
Table of Contents
- BLUF (Bottom Line Up Front)
- Executive Summary
- Credential Exposure
- Geopolitical Context
- Energy Grid Attack - DynoWiper (December 2025)
- January 2026 Events
- Campaign Analysis
- December 2025 to January 2026: Threat Landscape Overview
- MITRE ATT&CK Mapping
- Threat Actors
- Threat Actor Details
- Sources and References
- Confidence Levels
BLUF (Bottom Line Up Front)
In December 2025, russia-linked threat actors deployed DynoWiper against Polish energy infrastructure. ESET and Dragos linked the attack to Sandworm, while CERT Polska’s comprehensive report (January 30, 2026) attributed the infrastructure to Berserk Bear/Static Tundra. Throughout January 2026, 40+ pro-russian threat actors targeted 50+ Polish organizations across defense, energy, and government sectors. Key actors NoName057(16) and Z-PENTEST ALLIANCE have confirmed GRU ties per DOJ December 2025 indictments.
Executive Summary
Poland faces coordinated hybrid warfare operations combining destructive malware, sustained cyber activity and physical sabotage. This assessment covers January 2026 cyber operations, December 2025 DynoWiper attack and and past examples of physical sabotage.
The January operations show coordination beyond typical hacktivism: systematic sector rotation (between government, defence, and energy), multi-group same-day targeting, and timing correlated with geopolitical events. DDoS activity provides visible disruption while ICS access claims and ransomware represent more significant capability development.
Key Findings
| Finding | Details |
|---|---|
| DynoWiper attack | Russia-linked threat actors Berserk Bear (CERT atribution), Sandworm (ESET Atribution) deployed destructive wiper against Polish energy grid (Dec 2025) |
| Hybrid warfare surge | Fourfold increase in Russian sabotage operations in 2024; 219 incidents since 2014, 86% since 2022 |
| Scale | 40+ threat actors targeted 50+ Polish organizations |
| Defense targeting | 7 Polish Armaments Group subsidiaries targeted in 48 hours (13-14 JAN) |
| ICS/SCADA claims | 10+ access claims including heating systems, water treatment |
| Ransomware | 5 confirmed Polish victims (Dec 2025-Jan 2026) |
| State nexus | Key actors (NoName057(16), Z-PENTEST/CARR) GRU-linked per DOJ indictments |
| Credential exposure | 50,000+ Polish domain credentials identified in infostealer logs |
Key Assessments
| Assessment | Confidence | Basis |
|---|---|---|
| December 2025 attack was state-sponsored | HIGH | All sources (ESET, Dragos, CERT Polska) attribute it to Russian-linked state actors |
| Attribution dispute (Sandworm/Berserk Bear) reflects operational complexity | HIGH | Different data sources (malware, behavior, infrastructure) yield different conclusions |
| Operations are coordinated, beyond independent hacktivism | HIGH | Sequential sector targeting and multi-group same-day operations |
| Threat actors possess capabilities beyond DDoS | HIGH | Documented data exfiltration, ICS access claims, ransomware |
| State direction for key actors | HIGH | DOJ indictments confirm GRU funding/direction for CARR/Z-PENTEST, NoName057(16) |
| Timing correlates with geopolitical events | MODERATE | Activity surged after PM Tusk’s attribution and Polish Consulate Odessa strike |
Credential Exposure
Stolen credentials represent a persistent threat enabling future intrusions.
In a sample of recent infostealer logs, we identified credentials for 50,000+ Polish domains - companies, banks, healthcare, government, financial services, energy, defense.
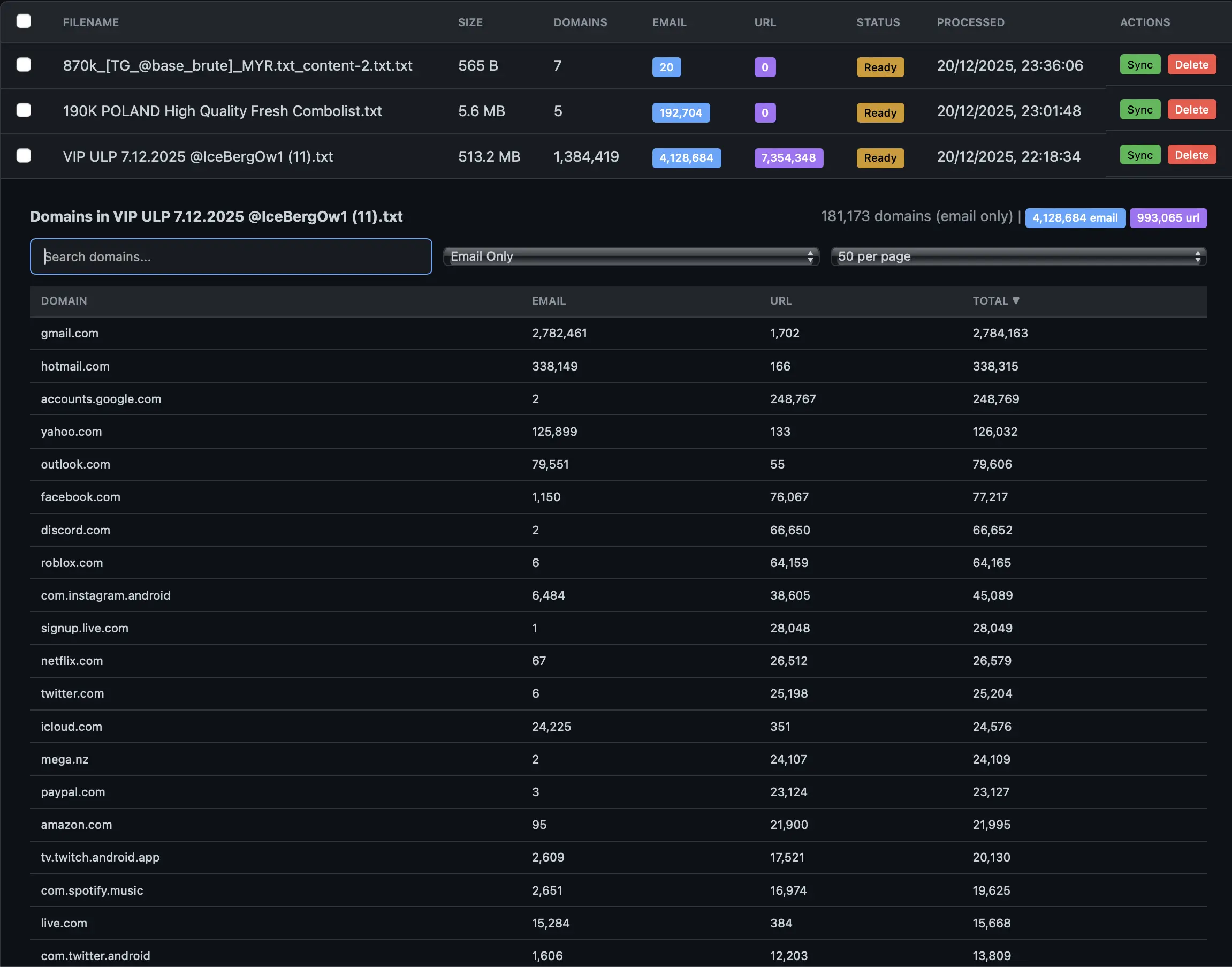 A single infostealer dump: 4.1 million credentials across 1.38 million domains.
A single infostealer dump: 4.1 million credentials across 1.38 million domains.
Polish credentials harvested by infostealers (RedLine, Raccoon, Vidar, LummaC2) are actively traded on Russian-language forums and Telegram. These credentials will be tested against Polish systems. Attackers exploit credential reuse across VPNs, email, cloud services, and internal systems.
Examples of Polish credential listings on Russian-language Telegram channels:
 Telegram channel sharing Polish credential dump
Telegram channel sharing Polish credential dump
 Telegram channel sharing Polish credential dump
Telegram channel sharing Polish credential dump
 Telegram post advertising Polish credentials
Telegram post advertising Polish credentials
 Telegram channel sharing Polish credential dump
Telegram channel sharing Polish credential dump
 Telegram credential channels are frequently banned, but new ones emerge within hours.
Telegram credential channels are frequently banned, but new ones emerge within hours.
Dark Web Activity Summary
Polish credential data is actively traded across multiple dark web forums and marketplaces. Activity levels observed in January 2026:
| Forum Type | Activity Level | Content |
|---|---|---|
| Telegram | VERY HIGH | Breach posts, credential dumps, combolist sharing |
| Russian clearnet forums | VERY HIGH | Breach posts, credential dumps |
| Breach forums | HIGH | Combolist sharing |
| Credential forums | HIGH | Unique combo posts |
| Dark markets | MODERATE | Fresh access sales |
| Carding forums | MODERATE | Admin access sales |
| Leak repositories | LOW-MODERATE | Database leaks |
Source: Baysec CTI dark web monitoring
Geopolitical Context
Russia’s Hybrid Warfare Campaign
Russia has dramatically escalated hybrid warfare operations against Poland and Europe since 2022. According to IISS analysis, sabotage operations increased four times in 2024 compared to previous years. GLOBSEC research documented 219 Russian hybrid warfare incidents since 2014, with 86% occurring since 2022.
Three Pillars of Russian Hybrid Warfare:

Examples from Poland:
Subversion - Spreading disinformation during Polish government elections.
Coercion - Belarus border crisis.
Sabotage - Marywilska fire, railway sabotage.
Physical Sabotage Timeline (2024-2026)
| Date | Operation | Details | Attribution | Source |
|---|---|---|---|---|
| May 2024 | Marywilska Shopping Center Fire | Warsaw’s Largest Shopping Center Destroyed; Over 1,400 Shops Affected, €500M+ in Damage | GRU | Notes From Poland |
| Nov 2025 | Railway Sabotage | FSB-directed sabotage via recruited Ukrainian proxies | FSB | BBC |
| Dec 2025 | Mirgorodsky Network | A 30-person FSB-directed sabotage network was disrupted, involving arson and reconnaissance activities. | FSB | Reuters |
| 29-30 Dec 2025 | Energy Grid Attack (DynoWiper) | Wiper malware deployed against CHP plants and renewable energy systems. The attack was unsuccessful. | Russia-linked | ESET, CERT Polska |
| Jan 2026 | Polish Consulate Odessa Strike | Russian missile strike on diplomatic facility | Russian military | Kyiv Post |
Marywilska Shopping Center Fire (May 2024):
On May 12, 2024, Warsaw’s largest shopping center was destroyed by arson. Polish government officially attributed the attack to GRU in May 2025:
- PM Donald Tusk: “We already know for sure that the large fire at Marywilska was the result of arson ordered by the Russian security services”
- Impact: 1,400+ shops destroyed, €500M+ damage
- Attribution basis: Lithuanian intelligence corroborated Polish findings
- Sources: Reuters, BBC, CNN

Marywilska Shopping Center fire, Warsaw, May 2024. Source: Reuters
Railway Sabotage (November 2025):
 FSB-directed railway sabotage in Poland, November 2025. Attack carried out via recruited Ukrainian proxies.
FSB-directed railway sabotage in Poland, November 2025. Attack carried out via recruited Ukrainian proxies.
Telegram Recruitment for Sabotage Operations
OCCRP investigation revealed that Russian intelligence services are actively recruiting European citizens via Telegram to conduct sabotage operations.
Anonymous Telegram channels lure people with payments of €500 to €2,000 for tasks ranging from graffiti to arson. Recruits are sent to carry out operations across several European countries, including Poland, Germany, France, Estonia, Latvia, Lithuania, and the Czech Republic, where they are tasked with arson, reconnaissance, infrastructure sabotage, and Molotov cocktail attacks.
Energy Grid Attack - DynoWiper (December 2025):
On December 29-30, 2025, Russian state actors deployed a previously undocumented wiper malware called DynoWiper against Polish energy infrastructure. The attack occurred on the 10th anniversary of Sandworm’s 2015 Ukrainian power grid attack.
| Attribute | Details |
|---|---|
| Attack Date | 29-30 December 2025 |
| Threat Actor | Russia-linked |
| Attribution | ESET/Dragos: Sandworm · CERT Polska: Berserk Bear/Static Tundra |
| Malware | DynoWiper (Win32/KillFiles.NMO), LazyWiper |
| Malware Type | Wiper - destructive data deletion |
| Impact | Unsuccessful - no service disruption confirmed |
Targets:
- Two combined heat and power (CHP) plants
- Renewable energy management systems (wind turbines and photovoltaic farms coordination infrastructure)
- RTU controllers (Mikronika), Moxa Nport devices
DynoWiper Technical Capabilities:
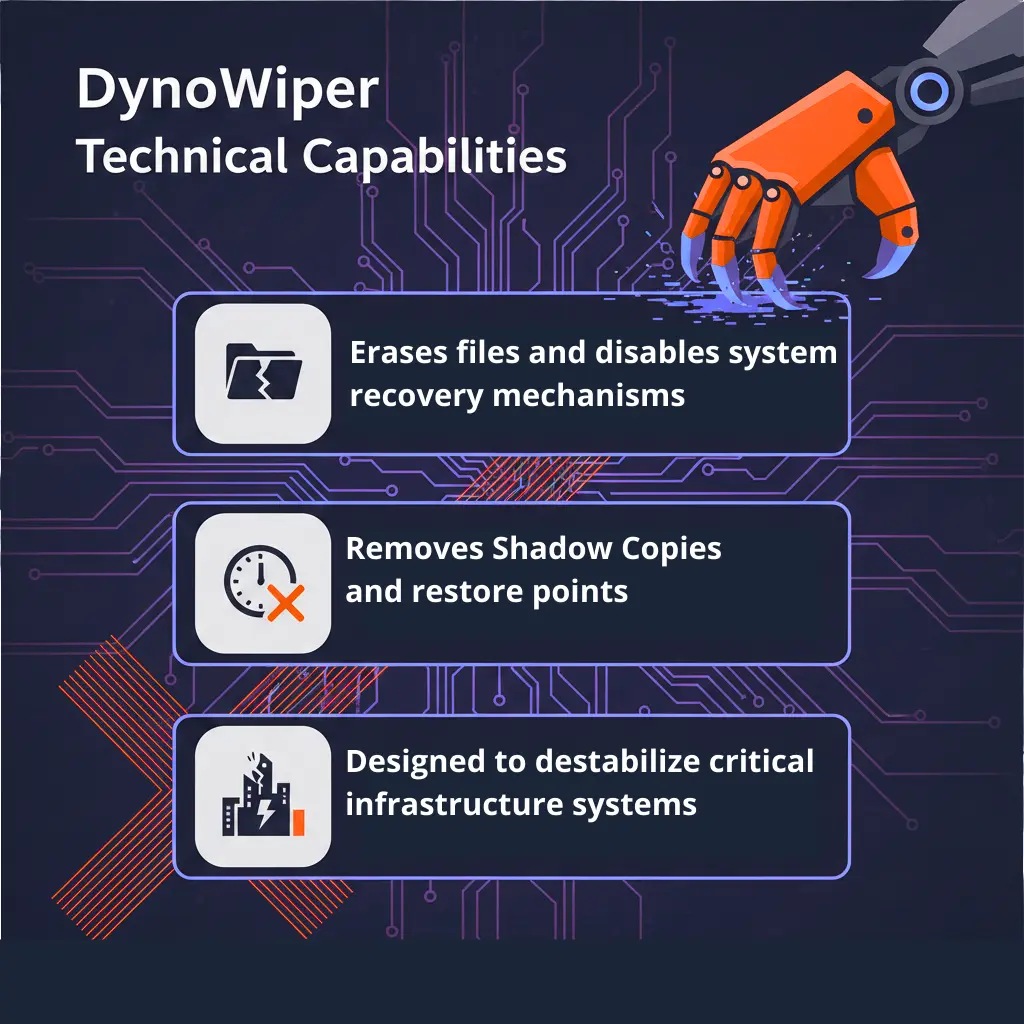 AI generated image using Google Gemini with modifications
AI generated image using Google Gemini with modifications
Conflicting Attribution:
On January 30, 2026, CERT Polska published comprehensive findings that arrived at a different conclusion than earlier commercial reporting. Three different intelligence perspectives produced two markedly different attribution conclusions:
- ESET attributes the observed activity to Sandworm, based on malware analysis that identified similarities between DynoWiper and previous Sandworm wipers, particularly those in the ZOV wiper family.
- Dragos links the activity to ELECTRUM/Sandworm through behavioral analysis, noting parallels with the cyber incidents that affected Ukraine’s power infrastructure in 2015 and 2016.
- CERT Polska associates the activity with Berserk Bear/Static Tundra, citing infrastructure analysis in which the command-and-control proxy network matches previously documented Berserk Bear infrastructure.
CERT Polska Findings (January 30, 2026):
CERT Polska’s analysis included visibility into initial access and network infrastructure that commercial vendors lacked:
- Attackers used compromised VPS servers and Cisco routers for command and control
- Infrastructure analysis matched proxy networks described by Cisco (Static Tundra) and FBI
- The proxy network overlaps significantly with known Berserk Bear/Dragonfly/Ghost Blizzard infrastructure
CERT Polska concluded that, based on the data collected, they cannot say for certain whether the actor behind the Sandworm cluster was involved in the attack in any way.
IOCs (CERT Polska):
| Type | Value | Context |
|---|---|---|
| SHA-256 | 8759e79cf3341406564635f3f08b2f33 3b0547c444735dba54ea6fce8539cf15 | DynoWiper |
| SHA-256 | f4e9a3ddb83c53f5b7717af737ab0885 abd2f1b89b2c676d3441a793f65ffaee | DynoWiper |
| SHA-256 | 835b0d87ed2d49899ab6f9479cddb8b4 e03f5aeb2365c50a51f9088dcede68d5 | LazyWiper |
| IP | 185.200.177[.]10 | VPN/O365 logons, DynoWiper execution |
| IP | 31.172.71[.]5 | Reverse proxy, data exfiltration |
| IP | 193.200.17[.]163 | VPN logons (multiple victims) |
Assessment: This attack represents the most significant cyber operation against Polish critical infrastructure in years. While the attack was unsuccessful, the attribution dispute between commercial vendors (Sandworm) and Poland’s national CERT (Berserk Bear/Static Tundra) highlights the increasing complexity of tracking state-sponsored cyber operations. From a defender’s perspective, resolving which specific Russian cluster was responsible matters less than understanding the attack methodology and implementing appropriate defenses.
*Sources: CERT Polska Report, ESET Research, Pylos Analysis,
January 2026 Events
Data suggests a correlation between geopolitical events and cyber activities in mid-January 2026. On 12–13 January, following the attack on the Polish Consulate in Odessa, there was a noticeable surge in DDoS activity. A few days later, on 15 January, after Prime Minister Tusk publicly attributed energy sector attack to Russia, the Server Killers campaign was observed targeting relevant systems. On 17 January, the transfer of MiG-29 aircraft prompted ICS-related claims, further illustrating the connection between significant geopolitical developments and targeted cyber responses.
In total 50+ Polish organizations were targeted across defense, energy, government, financial, and transportation sectors.
Consolidated Threat Actor Timeline
Over 40 distinct threat actors targeted Poland and other European countries in January 2026. The table below highlights the most significant activities targeting Poland during this period, derived from Baysec CTI:
| Date | Actor | Target/Activity | Attack Type |
|---|---|---|---|
| 02 JAN | NoName057(16) | Multiple polish targets | DDoS |
| 06 JAN | letchik | Polish Tax Firm | Unauthorized access (Claimed) |
| 06 JAN | The Flash DDoS BOX | Multiple polish targets | DDoS |
| 07 JAN | The Gentlemen | Wamtechnik | Ransomware |
| 08 JAN | Dark Storm Team | Government websites, Gas Distribution, PKP, KRUS | DDoS |
| 11 JAN | BD Anonymous | rozklad-pkp.pl, Ministry of Interior website | DDoS (Claimed) |
| 11 JAN | H4CKTHOR | Multiple Polish websites | DDoS |
| 12 JAN | Z-PENTEST ALLIANCE | Wastewater CCTV | ICS access |
| 13-14 JAN | NoName057(16) | 7 PGZ defense subsidiaries | DDoS (Attacks caused only temporary website unavailability) |
| 14 JAN | HEXROOTGROUP | Polish server for players | DDoS |
| 14 JAN | payoutsking | Chemirol | Ransomware |
| 14 JAN | NoName057(16)/DDoSia | TechnoAlpin Snow Production | ICS access (Claimed) |
| 15 JAN | Server Killers | Multiple government websites | DDoS |
| 15 JAN | Dark Storm Team | Olsztyn-Mazury Airport | DDoS (Claimed) |
| 17 JAN | BD Anonymous | BLIK | DDoS (Claimed) |
| 17 JAN | thelastwhitehat | PoradnikZdrowie | Data breach (Claimed) |
| 17 JAN | QuietSec | MTK-ACMO Heating Controllers | ICS access (Claimed) |
| 19 JAN | QuietSec | URE, PSE, ARE (Energy sector) | DDoS |
| 19 JAN | Z-PENTEST ALLIANCE | Industrial Dosing Equipment | ICS access (Claimed) |
| 22 JAN | QuietSec | e-podróżnik.pl, rozkład-pkp.pl (Polish travel portals) | DDoS |
Verification: Claimed = threat actor post only
Source: Baysec CTI
ICS/SCADA Access Claims
10+ claims of unauthorized access to Polish industrial control systems.CISA Advisory AA25-343a warned about pro-Russian groups active targeting of ICS via VNC exploitation and default credentials.
| Date | Target | Actor | Risk | Verification |
|---|---|---|---|---|
| 17 JAN | MTK-ACMO Heating Controllers | QuietSec | High | Claimed (Telegram post) |
| 19 JAN | Industrial Dosing Equipment | Z-PENTEST ALLIANCE | High | Claimed (Telegram post) |
| 02 JAN | Wastewater Treatment Management | Z-PENTEST ALLIANCE | High | Assessed (TTP match) |
| 15 JAN | Water Treatment Station | Z-PENTEST ALLIANCE | High | Assessed (TTP match) |
| 12 JAN | Wastewater Treatment Plant CCTV | Z-PENTEST ALLIANCE | Moderate | Claimed (Telegram post) |
| 15 JAN | Boiler Management System | NoName057(16)/DDoSia | Moderate | Assessed (TTP match) |
Verification Key:
- Claimed = Threat actor posted evidence (screenshots/video) on Telegram - not independently verified
- Assessed = Attribution based on TTP alignment with CISA AA25-343A
Note: Z-PENTEST ALLIANCE is the primary water/wastewater sector threat actor per Cyble 2025 Threat Landscape Report. These are threat actor claims - actual ICS compromise has not been independently confirmed.
ICS Exploitation Methodology (CISA AA25-343A)
According to CISA Advisory AA25-343A, pro-Russian hacktivist groups employ the following TTP chain to compromise ICS/SCADA systems:
Attack Chain:
| Step | Technique | MITRE ID | Description |
|---|---|---|---|
| 1 | Scan for vulnerable devices | T0883, T1595.002 | Use internet-scraping tools (Nmap, OPENVAS) to find VNC services on ports 5900-5910 |
| 2 | Initiate temporary VPS | T1583.003 | Spin up disposable infrastructure to execute brute force attacks |
| 3 | Access via VNC | T1021.005 | Connect to hosts using VNC remote desktop software |
| 4 | Confirm connection | T0886 | Verify access to vulnerable device |
| 5 | Brute force credentials | T1110.003 | Use password spraying tools against default/weak credentials |
| 6 | Gain HMI access | T0883, T0812, T0859 | Access Human-Machine Interface with default or no passwords |
| 7 | Manipulate via GUI | T0823 | Use HMI graphical interface to modify system parameters |
| 8 | Cause impact | T0828, T0829, T0836 | Modify settings, disable alarms, cause loss of view |
HMI Manipulation Actions (observed):
- Modify usernames/passwords (T0892) - operator lockout
- Modify parameters and setpoints (T0836) - process disruption
- Modify device/instrument settings (T0831) - calibration tampering
- Disable alarms (T0878) - hide intrusion/effects
- Create loss of view (T0829) - force manual intervention
- Device restart/shutdown (T0816) - service disruption
What Makes These Attacks Successful:
- VNC services exposed to internet on default ports
- Default or weak credentials on HMI devices
- Lack of MFA on critical control systems
- No network segmentation between IT and OT
- Insufficient monitoring of OT access attempts
Assessment: These actors show limited technical sophistication, yet they can still cause real harm. According to CISA, they often misunderstand the systems and processes they target, but their willingness to interfere with critical infrastructure creates real safety risks.
Campaign Analysis
Coordination Evidence
The January 2026 campaign shows indicators of coordination rather than independent hacktivism:
1. Sequential Sector Targeting:
- Week 1 (01-07 JAN): Government services
- Week 2 (08-14 JAN): Defense industrial base and ransomware attacks
- Week 3 (15-20 JAN): Energy sector and ICS probing
2. Multi-Group Same-Day Operations:
- 08 JAN: Dark Storm Team - 5 targets
- 12 JAN: 4 groups, 7+ targets
- 15 JAN: Server Killers + Dark Storm - 9+ targets
3. Geopolitical Correlation:
| Date | Event | Cyber Activity |
|---|---|---|
| 12-13 JAN | Polish Consulate Odessa struck | DDoS surge |
| 15 JAN | Tusk attributes energy attack to Russia | Server Killers campaign |
| 17 JAN | MiG-29 transfer confirmed | QuietSec ICS claims |
DDoS Campaign Assessment
Attack Volume by Actor (January 2026):
| Actor | Claimed Attacks | Primary Targets | Peak Activity |
|---|---|---|---|
| NoName057(16) | 30+ | Defense, Regional Gov | 13-14 JAN |
| Dark Storm Team | 10+ | Government, Transport | 08 JAN |
| Server Killers | 7 | Government Services | 15 JAN |
| BD Anonymous | 6 | Government, Financial | 11, 17 JAN |
| QuietSec | 6 | Energy, ICS | 17, 19 JAN |
Attack Verification:
- Actors use check-host.net for public verification
- Some claims are exaggerated or unverifiable
- Actual downtime varies from minutes to hours
Pattern Analysis: Threat Actor Coordination
Evidence of Coordination:
| Pattern | Observation | Assessment |
|---|---|---|
| Temporal clustering | Multiple groups attack same day (08, 12, 15 JAN) | Coordinated campaign timing |
| Target overlap | Ministry of Interior hit by 3 groups | Shared targeting intelligence |
| Sector rotation | The attacks targeted multiple sectors, spanning government, defense, and energy | Planned campaign phases |
| Telegram cross-posting | DDoSia forwards Z-PENTEST claims | Operational relationship |
| Capability layering | DDoS, ICS, and ransomware groups | Multi-vector coordination |
Communication Patterns:
- NoName057(16) and Z-PENTEST ALLIANCE share content via Telegram
- DDoSia Project forwards ICS access claims from affiliated groups
- Attack announcements often appear within hours of each other
Assessment: The campaign structure suggests central coordination rather than independent hacktivist activity.
December 2025 to January 2026: Threat Landscape Overview
Poland faced a sharp rise in cyberattacks at the start of 2026. In December 2025, roughly 15 threat actors were targeting the country, but by January, that number had more than doubled, with over 40 actors active in the region. NoName057, shifted its focus from France, Belgium, and Denmark in December to launch more than 30 attacks on Polish targets in January alone.
In January 2026 Activity targeting industrial control systems (ICS/SCADA) also picked up, with over 10 confirmed access attempts recorded. The defense sector experienced concentrated attacks, as seven subsidiaries of PGZ were hit within just 48 hours.
The data point to a clear escalation in both the number of attackers and the intensity of their operations, underlining growing threats to Poland’s infrastructure and critical industries.
Source: Baysec CTI
MITRE ATT&CK Mapping
Enterprise Techniques
| Technique ID | Name | Threat Actors |
|---|---|---|
| T1498 | Network Denial of Service | NoName057(16), Dark Storm, Server Killers, QuietSec |
| T1499 | Endpoint Denial of Service | NoName057(16), Dark Storm |
| T1078 | Valid Accounts | QuietSec, Sector16, Z-PENTEST ALLIANCE |
| T1213 | Data from Information Repositories | QuietSec, aiyewumi |
| T1567 | Exfiltration Over Web Service | thelastwhitehat, aiyewumi |
| T1486 | Data Encrypted for Impact | THE GENTLEMEN, payoutsking |
| T1583.003 | Acquire Infrastructure: VPS | Z-PENTEST ALLIANCE, Sector16 |
| T1595.002 | Active Scanning: Vulnerability Scanning | Z-PENTEST ALLIANCE, Sector16, NoName057(16) |
| T1021.005 | Remote Services: VNC | Z-PENTEST ALLIANCE, Sector16, QuietSec |
| T1110.003 | Brute Force: Password Spraying | Z-PENTEST ALLIANCE, Sector16 |
| T1591 | Gather Victim Org Information | Z-PENTEST ALLIANCE, Sector16 |
ICS/OT Techniques (per CISA AA25-343A)
| Technique ID | Name | Threat Actors | Use |
|---|---|---|---|
| T0883 | Internet Accessible Device | Z-PENTEST ALLIANCE, Sector16, QuietSec | Gain access through internet-exposed HMI devices |
| T0812 | Default Credentials | Z-PENTEST ALLIANCE, Sector16 | Build libraries of known default passwords for control devices |
| T0859 | Valid Accounts | Z-PENTEST ALLIANCE, Sector16, QuietSec | Use password guessing tools to access legitimate accounts |
| T0886 | Remote Services | Z-PENTEST ALLIANCE, Sector16, QuietSec | Leverage VNC services to access system HMI devices |
| T0823 | Graphical User Interface | Z-PENTEST ALLIANCE, Sector16, QuietSec, NoName057(16) | Interact with HMI devices via GUIs to modify control devices |
| T0816 | Device Restart/Shutdown | Z-PENTEST ALLIANCE, NoName057(16) | Turn off HMIs during intrusion |
| T0878 | Alarm Suppression | Z-PENTEST ALLIANCE, NoName057(16) | Use HMI interfaces to clear alarms caused by activity |
| T0892 | Change Credential | Z-PENTEST ALLIANCE, Sector16, QuietSec | Change HMI usernames/passwords for operator lockout |
| T0836 | Modify Parameter | Z-PENTEST ALLIANCE, NoName057(16) | Change operational device limits from HMI |
| T0855 | Unauthorized Command Message | Z-PENTEST ALLIANCE | Send unauthorized commands to control system assets |
| T0828 | Loss of Productivity and Revenue | Z-PENTEST ALLIANCE, Sector16, QuietSec, NoName057(16) | Purposefully impact productivity and create costs |
| T0829 | Loss of View | Z-PENTEST ALLIANCE, QuietSec | Change credentials preventing remote process modification |
| T0831 | Manipulation of Control | Z-PENTEST ALLIANCE, NoName057(16) | Change setpoints impacting process efficiency |
Threat Actors
Key Groups Active in January 2026
| Actor | Attacks | Primary TTPs | State Nexus |
|---|---|---|---|
| Sandworm/Berserk Bear | 1 (Dec 2025) | DynoWiper, infrastructure destruction | Russia-linked (disputed) |
| NoName057(16) | 30+ | DDoSia botnet, Layer 7 DDoS | GRU-linked (DOJ Dec 2025) |
| Z-PENTEST ALLIANCE | 5 ICS claims | VNC exploitation, SCADA access | GRU-linked Unit 74455 (CISA AA25-343a) |
| QuietSec | 6 | DDoS, ICS claims, data exfiltration | Pro-Russian |
| Dark Storm Team | 10+ | DDoS, defacement | Pro-Russian/Pro-Palestinian |
| Server Killers | 7 | Layer 7 DDoS | Pro-Russian |
| BD Anonymous | 6 | DDoS | Pro-Russian |
| HEXROOTGROUP | 1+ | DDoS, defacement | Pro-Russian |
| H4CKTHOR | 3+ | DDoS | Hacktivist |
| The Flash DDoS BOX | 1+ | DDoS-for-hire | Criminal (DDoS-as-a-Service) |
| Infrastructure Destruction Squad | 1+ | DDoS | Pro-Russian |
Ransomware Operators
| Actor | Victim | Date |
|---|---|---|
| SafePay | polhun.pl | 25 DEC 2025 |
| LockBit 5 | mostykatowice.pl | 30 DEC 2025 |
| THE GENTLEMEN | Wamtechnik | 07 JAN |
| payoutsking | Chemirol | 14 JAN |
Source: Baysec CTI
Threat Actor Details
For organizations seeking a deeper understanding of the threat landscape, our team of cybersecurity experts can provide a comprehensive report on the threat actors outlined above.
The report includes detailed profiles, technical indicators, tactics, techniques, and procedures (TTPs), as well as historical activity and patterns that may impact business operations.
Access to threat actor analysis delivers actionable intelligence on emerging threats, enabling informed risk assessment and the enhancement of organizational cybersecurity posture. Reports are customized, ensuring the insights are relevant, timely, and practical for strategic decision-making.For more information or to request a full report, please contact us at: kontakt@baysec.eu
Sources and References
Government & Law Enforcement
- CERT Polska. Raport Incydent Sektor Energii 2025. January 30, 2026.
- CISA. AA25-343A: Pro-Russia Hacktivists Conduct Opportunistic Attacks Against US and Global Critical Infrastructure. December 2025.
- US Department of Justice. Justice Department Announces Actions to Combat Two Russian State-Sponsored Cyber Criminal. December 2025.
- Europol. Global Operation Targets NoName057(16) Pro-Russian Cybercrime Network. 2025.
- FBI IC3. Static Tundra/Berserk Bear Proxy Infrastructure Advisory. August 2025.
- CERT Polska. Polish National CERT Advisories and Incident Reports.
Think Tanks & Research
- GLOBSEC. How Russia’s Hybrid Warfare Will Escalate in 2026. 2026.
- IISS. The Scale of Russian Sabotage Operations. August 2025.
- Cyble. Critical Infrastructure Attacks Became Routine for Hacktivists in 2025. 2025.
News & Investigative Journalism
- Reuters. PM Tusk Attributes Energy Attack to Russia. January 15, 2026.
- Notes From Poland. Poland Confirms Russia Behind Marywilska Fire. May 12, 2025.
- OCCRP. Make a Molotov Cocktail: How Europeans Are Recruited Through Telegram to Commit Sabotage, Arson, and Murder. 2025.
- BBC. Poland Railway Sabotage (FSB Attribution). November 2025.
- Euronews. Poland Accuses Russia of Marywilska Arson. May 12, 2025.
- Kyiv Post. Polish Consulate Odessa Strike. January 2026.
Threat Intelligence
- Baysec CTI. Primary Threat Intelligence Platform. Internal.
- ESET Research. Sandworm DynoWiper Attack on Poland Power Grid. January 2026.
- Pylos. Attributive Questions in High-Profile Incidents. January 31, 2026.
- Cisco Talos. Static Tundra (Berserk Bear) Infrastructure Analysis. 2025.
- The Hacker News. New DynoWiper Malware Used in Attempted Attack. January 2026.
- Security Bez Tabu. DynoWiper - Poland Energy Sector Attack. January 2026.
- Ransomware.live. THE GENTLEMEN Group Profile. 2025.
- Cybereason. THE GENTLEMEN Ransomware Analysis. 2025.
- SOCRadar. NoName057(16) and DDoSia Analysis. 2025.
- Picus Security. How NoName057(16) Uses DDoSia to Attack NATO Targets. 2025.
Confidence Levels:
- CONFIRMED: Multiple independent sources, government attribution
- ASSESSED: Technical indicators align with known patterns
- CLAIMED: Threat actor statement only, unverified
